DoD ASSIST
STACK · Axure RP · Figma · Adobe Creative Cloud§ 01Context
ASSIST is the Department of Defense's official repository for defense and federal specifications, standards, and technical documents. Military acquisition specialists, defense contractors, and government personnel rely on it to find the document that governs a specific component, material, or process, often under deadline, often across both classified and unclassified material.
§ 02The problem
The legacy platform had grown into hundreds of data fields, unclear workflows, and outdated interfaces. Submission, search, and document management each ran on their own conventions, creating friction for the people who actually had to navigate the system to do their job. The redesign had to simplify complex submission and retrieval processes while maintaining strict security compliance for classified and unclassified documents alike.
§ 03Approach
- 01
Conducted stakeholder and user interviews with defense contractors and government personnel. Mapped real workflows, pain points, and security requirements end to end.
- 02
Built personas and journey maps showing how each user type accessed technical standards across a procurement cycle.
- 03
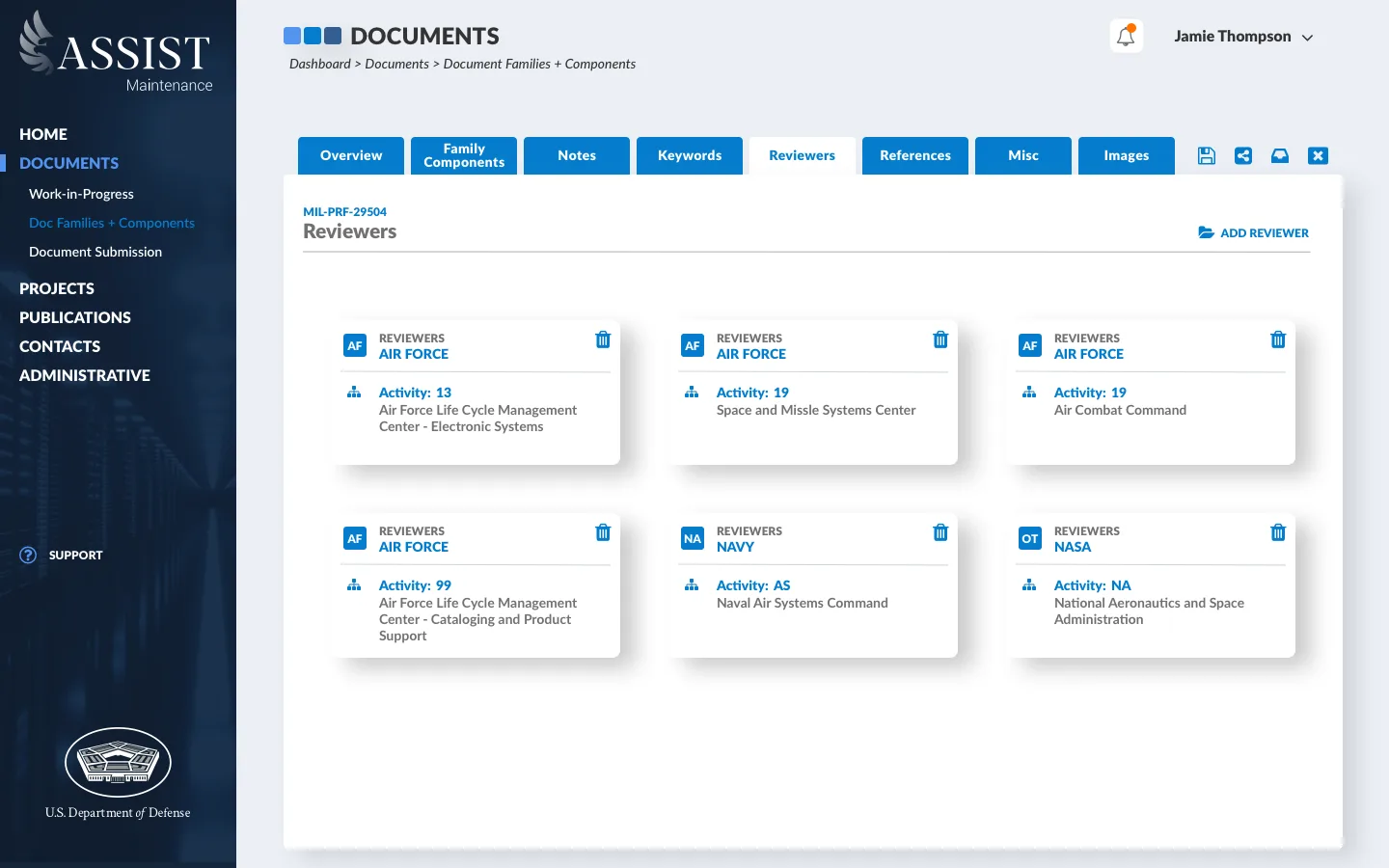
Redesigned the information architecture for document search, submission, and lifecycle management as a single coherent system, not three siloed surfaces.
- 04
Produced wireframes and high-fidelity prototypes, tested with actual users under operational constraints. Refreshed the visual identity and shipped a comprehensive design system.
§ 04Selected artifacts
Artifacts shown below are placeholders. Cleared, sterilized screens will be supplied for each.
 INFO ARCH
INFO ARCH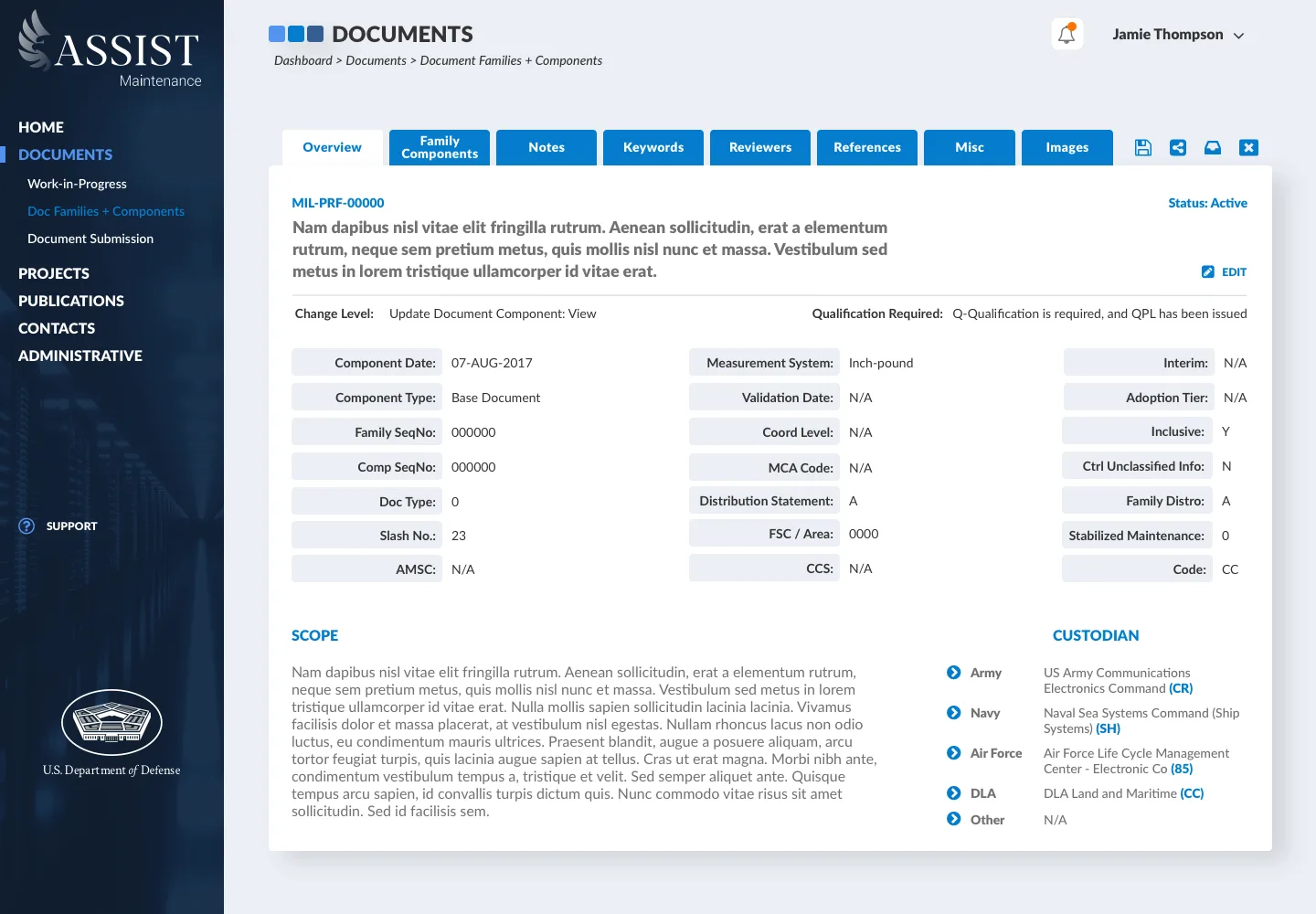 HI-FI
HI-FI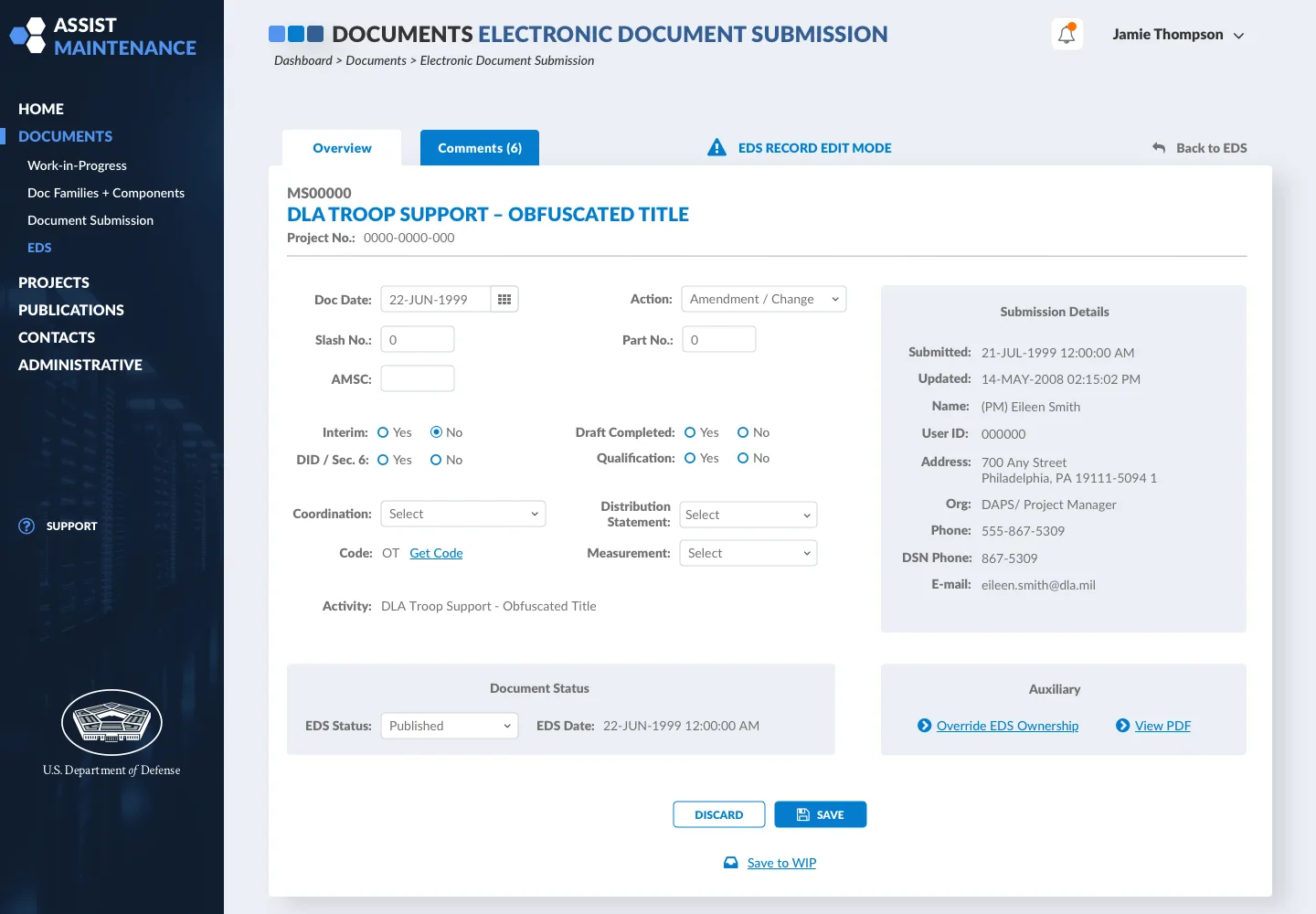 HI-FI
HI-FIDelivered a modernized, secure system for managing defense standards. The redesign demonstrated that highly regulated government systems serving sensitive operations can provide intuitive, efficient user experiences without compromising security protocols.
§ 06Reflection
Defense systems do not require complex interfaces to be secure. Clear information architecture and modern interaction patterns coexist with the strictest security requirements when the constraints are designed around, not around-up.
